Take your AEM Infrastructure from zero to hero in AWS with CloudFormation

We love to work with Adobe Experience Manager (among others) and create new infrastructure environments for our clients. Usually, manual deployment of the AEM stack and adjacent software is required to provide a proper service. The growing demand pushed us to rethink our delivery process, all with the goal of delivering the same quality in a shorter period of time.
Since 2017, Netcentric has been working on the infrastructure as a code to ease and improve our delivery times for our clients. We based our efforts on Amazon CloudFormation with support for Puppet to deploy all the software, tools, security policies, updates, etc.
Let’s talk a bit about our solution.
When you initially look at the code it can be overwhelming, but we assure you that it’s not difficult at all. Actually, everything has a purpose and everything is documented so you’ll never get stuck.
The framework we have created is very useful for organizations who want to host the Adobe Experience Manager stack on Amazon Web Services (AWS) and avoid potential headaches during the implementation (including all the VPCs, Security Groups to create, Load Balancers, EC2 Instance, etc.). Our framework can even create a direct VPN connection with your organization.
It also offers a certain amount of flexibility. For example, your organization has started with a 1:2:2 setup and wants to upgrade to a 1:3:4 setup? If you have used our framework, you only need to add a few lines of code to the root stack and update the current CloudFormation Stack — it’s that easy. A little heads up, if a configuration management tool is required, such as Puppet or Ansible, you’ll have to use it to deploy the AEM and all the necessary tools/software to the newly provisioned instances (our config management by choice is Puppet under which all functionality is supported).
To get started you’ll have to create the main file (you can create multiple, for separate settings for each environment) where you declare all the resources directly or by referencing stacks provided by the framework. When you consider that all the resources are declared, you just need to deploy the main file via the command line.
Out of the box our framework has, amongst others, the following features:
- ALB setup with granular settings
- Automated EBS backups
- Automated uptime (start/stop instances using schedules)
- Certificate Management
- Configurable resource naming
- Custom tagging (e.g. to feed config management tools or firewalls)
- EC2 Instance creation with custom EBS settings
- Route53 DNS management, locally and remotely (in a different account)
- Support for fully encrypted setups (full HTTPS + EBS encryption)
- Support for provisioning with Ansible
- Support for provisioning with Puppet (AWS Opsworks)
- Support for various setups (from 1:1:0 up to 1:3:3)
- VPC creation (with all its subcomponents)
- VPC peering
- VPN creation (AWS side) using Transit Gateways
- VPN creation (AWS side) using VPN Gateways

Example of the example.yaml used to generate the infrastructure
Please check out our example.yaml on GitHub and get comfortable with the parameters you can set up for your environment provisioning. In the README.md file from the GitHub repository, you can find the prerequisites to get you started with the framework.
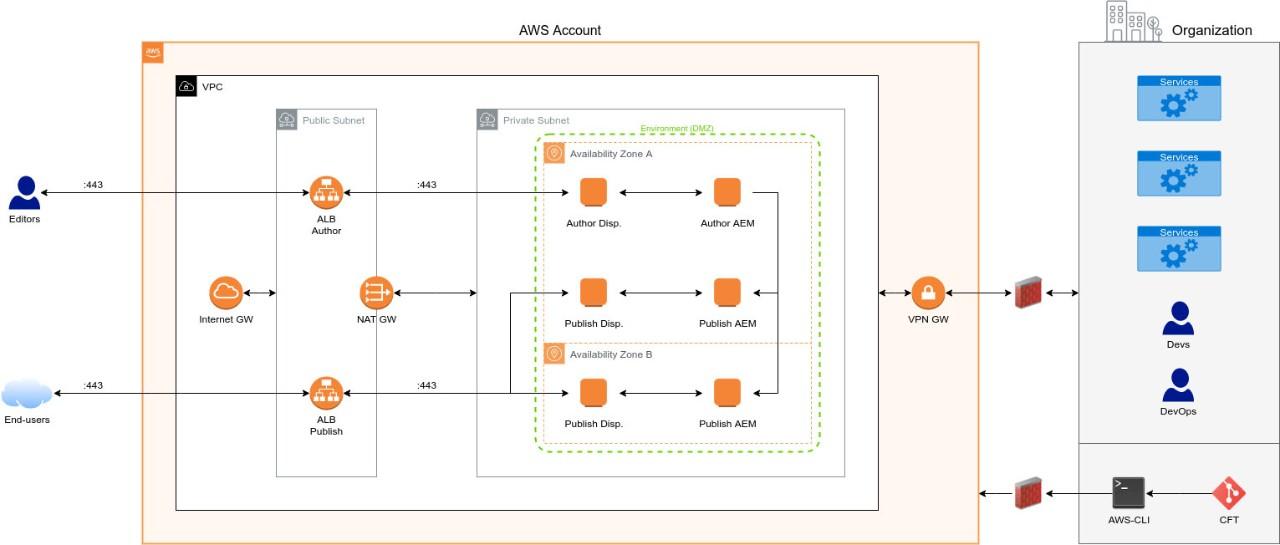
A high-level diagram of a possible setup
A high-level diagram of a possible setup
Take a look at the high-level diagram above. From a big picture perspective, this shows you how the infrastructure is created and how it’s interacting with its components. In the end, all AWS infrastructure components can be customized based on your requirements and needs, such as adding a CDN or the service of your definition.
Rely on our expertise
We’re confident our framework will enable you to set up your environment provisioning headache-free. But, if you need a helping hand, or you’d like to find out more about the benefits of leveraging AWS with CloudFormation — get in touch with our experts.